The manufacturing sector has witnessed and continues to witness a significant increase in targeted cyber attacks as a result of increased integrated systems connecting all organisational levels from the shop floor to C-suite. As such, the sector is reinforcing their cyber security posture by introducing and upgrading technology capabilities. However, one area is consistently overlooked: Securing the supply chain. According to Accenture Security1, indirect attacks against weak links in the supply chain now account for 40% of security breaches of which 63% faced losses of up to £5,0002. In this week’s blog I explore why the manufacturing supply chain is being targeted, alongside actionable advice to best protect your business.
Why is the supply chain a target?
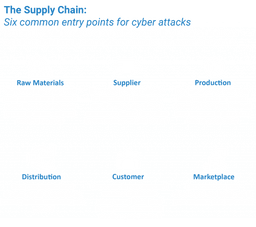
Cyber criminals are targeting manufacturing supply chains to reach multiple businesses with their malware through a singular attack. As such, threat actors are identifying strategically important suppliers, due to their poor IT infrastructures, procedures, and access to critical data and internal systems which wouldn’t be accessible through traditional attack vectors. Recent research conducted by Ponemon Institute found that the average organisation had given 471 third parties access to sensitive information3. Due to the interconnected network environments that manufacturers operate within, if any element is breached, constituent members are at risk. Therefore, the supply chain security cannot simply be viewed as an internal IT problem alone and must be addressed coherently across the whole supply spectrum.
Failure to act now could result in significant ramifications including; reputation damage, loss in contracts, a halt in production and even liquidation. In recent months alone data breaches within supply chains included high-profile cases such as the Colonial Pipeline and SolarWinds which impacted over 100 companies. These attacks are the most recent reminders that cyber security is a core supply chain issue and a threat that is increasingly growing in frequency and severity. Thus, threat actors are systematically disrupting the manufacturing sector through indirect supply chain organisations as a gateway to access high-value targets, due to their poor security posture.
Secure your supply chain
The first step in securing your supply chain is to understand the risks. Until a holistic picture of your supply chain is established, it will be very difficult to recognise any meaningful control over it. It is imperative to understand who your suppliers are, the value of your information which they hold and the level of access they have3. As such, it is recommended that a Cyber Due Diligence Audit is conducted at periodic intervals to identify vulnerabilities within existing suppliers and also new suppliers.
Secondly, encourage suppliers to continue improve and develop their security practices and procedures. The Centre for the Protection of National Infrastructure (CPNI)3 highlights the importance of “advising and supporting suppliers as they seek to make improvements to their IT infrastructure. Empathising how an improved cyber security infrastructure may enable suppliers to compete for and win future contracts”. As such, ensuring suppliers comply with recognised security standards and certification schemes i.e. ISO 270001: 2013 Information Security Standards and Cyber Essentials Plus will showcase suppliers security control systems.
Finally, meet your own responsibilities as a supplier. Investing into a Managed Service provider, such as KryptoKloud will significantly alleviate an organisations cyber security concerns, reduce risk, put you back in control, allow you to continue to operate your business effectively and give you peace of mind for your own well-being.
To conclude, the list of reasons why manufacturers should integrate control systems across the supply chain are very compelling. However, with more third parties having access to corporate information, the sector is exposing themselves to cyber risks which cannot be controlled by traditional IT teams. As such, investing in appropriate policies and procedures alongside CYDD audits and installing additional security features will allow the sector to operate cohesively, reducing vulnerabilities across the supply chain.
End notes
2. https://www.makeuk.org/insights/reports/cyber-security-for-manufacturing